Unlock Your Digital Future
To be a true business enabler, technology should be part of your overall strategy, not an afterthought.
Ready to unlock your digital future?
These companies trust ProServeIT to help unlock their digital future.

















Copilot for Microsoft 365 is available for businesses of all sizes!
Copilot for Microsoft 365 is your go-to AI-powered assistant that transforms the way you work. It uses large language models (LLMs) and your organization’s data to provide real-time intelligent assistance.
Working alongside the Microsoft 365 applications such as Teams, Word, Outlook, PowerPoint and Excel, your organization can enhance productivity, amplify creativity, and confidently rely on using responsible, secure AI, all while maintaining the flow of work.
Copilot makes an impact on productivity, creativity, and time.
70%
of early Copilot users said they were more productive.
68%
said Copilot helped them jump-start the creative process.
85%
of users said Copilot reduced effort to complete their tasks.
*Source: Microsoft Work Trend Index Special Report, November 15, 2023.
What Can Copilot’s Earliest Users Teach Us About Generative AI at Work.
Start Your Organization's AI Journey
Choose your path to success that suits your organization's needs and preferences with our innovative AI solutions. Whether you’re creating a strategic AI roadmap, seeking rapid value through a pilot program, or waiting for the right opportunity, we’ve got you covered. Wherever you begin, rest assured that we provide the tools and resources to guide you every step of the way.
Explore How Our Modern Technology Framework Can Help Your Organization
Our Modern Technology Framework
In the age of disruption, you win when (and only when) you have a solid technology framework and have IT as part of your overall business strategy.
A solid technology framework includes the following components: Insights & Automation, Core Business Application, Productivity, Brand Experience, Departmental Applications, Infrastructure, and Cybersecurity. Does your framework include all seven? Scroll down. Have a read. When you are ready, we are here to chat.
-


Cybersecurity
Make cybersecurity the foundation of your entire organization.
-
Infrastructure
Manage IT infrastructure proactively.
-
Productivity
Choose the right productivity tools that support your employees.
-
Brand Experience
Create a stellar brand experience for your employees and customers.
-
Business Applications
Strike a perfect balance between your business objectives and IT capabilities.
-

Insights & Automation
Be efficient with your time through insights & automation.
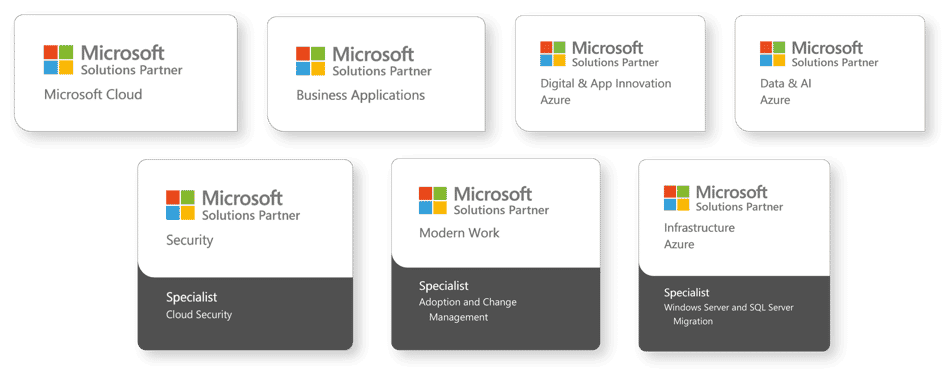
We have extensive experience in high-demand Microsoft Cloud Solution areas to help you with your digital transformation.
 ProServeIT Puts Security First!
ProServeIT Puts Security First!
We are pleased to announce that ProServeIT has recently joined Microsoft's elite Managed Security Solutions Provider (MSSP) program. This invitation-only program is for top Microsoft Partners who have demonstrated exceptional expertise in cybersecurity solutions, recognizing ProServeIT's advanced qualifications for Microsoft security solutions.
Furthermore, we are a member of Microsoft's Intelligent Security Association (MISA), which is comprised of a network of independent software vendors (ISV) and managed security service providers (MSSP) who have combined their solutions with Microsoft's security technology to better protect against a world full of growing cyberthreats.
Grow Your Technology Knowledge with ProServeIT Academy!
Join online classes. Level up your skills. Enjoy special offers and big savings!
We're back with more content, more learning and more networking! ProServeIT Academy is proud to present our new line-up for virtual learning.
Our new online classes includes presentations, demos, roundtable discussions, fireside chats, and Q&A's.
There are courses for everyone from IT stakeholders, CEOs and their executive team, Line of Business Leaders (Finance, Sales, Marketing, Operations Leaders), HR leader, and anyone else who'd like to learn about how technology strategy should be fully integrated with business strategy.

Click any course below to access complimentary class recordings. ⬇
Solutions in High Demand

Copilot for Microsoft 365

Alarm Guardian

Dynamics 365
 We believe in using business as a force for good.
We believe in using business as a force for good.
Certified B Corporations are part of a growing movement of people using business as a force for good. Across over 95 countries in over 160 industries, over 8,000 companies are putting people and the planet before profits and redefining what it means to be successful in business.
ProServeIT is immensely proud of becoming a B Corp and deeply committed to making the world a better place with technology. We've been doing this work over the last 20 years and will continue to do so. To us, a B Corp certification is more than a stamp of approval. It is our culture, our lifestyle.
To learn more about ProServeIT’s B Corp Certification, visit our official profile on B Corporation website.
 ProServeIT is on the list! Canada's Top Small & Medium Employers for 2024
ProServeIT is on the list! Canada's Top Small & Medium Employers for 2024
We have been recognized by Mediacorp Canada Inc. and The Globe and Mail as one of Canada’s top Small & Medium Employers for 2024.
Insightful Readings: Explore Our Blog Posts
Get the latest news and trends on artificial intelligence.
Frequently Asked Questions
These are some of the most frequently asked questions. If your questions are not addressed here, please contact us at cloud@proserveit.com.
What does digital transformation mean to businesses?
Digital Transformation, the process of integrating digital technology into all areas of your business, is a key component of ensuring that you are operating your business at peak efficiency and productivity, and providing valuable improvement to the customer experience and overall customer satisfaction. In the age of disruption, digital transformation is becoming more and more necessary for organizations to be more agile, competitive, customer-centric, and flexible.
How can ProServeIT help me with my digital transformation?
ProServeIT's holistic approach and modern IT framework provide you with the roadmap and tools necessary to explore digital transformation from start to finish. From determining the best ways to increase productivity, to providing a better end-user experience and the right applications for your business, to making the most of your data, automating tedious and menial tasks to provide better overall job satisfaction, and ensuring that security and infrastructure are taken into account at every turn, ProServeIT is your go-to IT partner in taking you where you want to go. Book a call and get started!
What are the benefits of working with ProServeIT?
At ProServeIT, we have three main differentiators that provide benefit to our customers:
- We are a full-stack technology partner and take a holistic approach to making sure that IT is a business enabler. We'll be with you from start to finish, helping you along every aspect of your digital transformation journey to the Cloud.
- We make sure you've got the technology you need, when you need it, and once you've purchased it, you're getting the maximum ROI. We place special emphasis on ensuring that your business needs and IT requirements are in complete alignment.
- We put a security lens on everything that we do. We help you manage your advanced cybersecurity risks and secure your identity, data, and devices. We also implement this internally, so when you're a customer of ours, we're keeping your data safe.
What are the benefits and drawbacks of outsourcing IT services? How can I get started with Managed IT Services?
There are several benefits of outsourcing IT services, like taking better control of your organization's costs, receiving 24/7/365 support, or proactively managing your cybersecurity needs and requirements. Although the perception is that hiring a Managed IT Services Provider would take away jobs, outsourcing IT Services actually frees up your team to tackle more important, business-oriented tasks. Learn more about the benefits of engaging with a Managed IT Services Provider with this free eBook, and then book a call to talk about how you can get started.
I'm a current customer. How do I open a service ticket?
To open a service ticket, please email a description of the issue you're experiencing to help@proserveit.com and our experienced team will get started on helping you solve your issue. It is also recommended that you summarize the issue you're experiencing in the subject line of your email.
Who do you serve? Geographic regions, industries, and the size of organizations?
We have the capability to assist small organizations with 50+ employees to large enterprises in any industry and located throughout Canada and the United States of America. Here are just some of the customers we serve:
Small organizations: WWF, The Mastercard Foundation, Chudleighs, HTS Engineering, Winnermax Capital, Tim Hortons Foundation Camps, Pet Health
Large Enterprises: Maple Leaf Sports and Entertainment, KPMG, Mattamy Homes, The Woodbridge Group, Goodlife Fitness, The ALDO Group, Toys R Us, Wajax
Click here to see case studies and testimonials.
How can I contact you if my questions aren't answered here?
We're always available at cloud@proserveit.com. Reach out and let's chat!