5 Tips for Vendor Risk Management: Protect Your Organization
There are numerous security products available on the market but understanding which ones are right for your environment can be a challenge. To make it even more complicated, some Microsoft security products now have new names.
In this blog post, we will discuss new Microsoft names for some of their security products, what Microsoft Sentinel is and explore a few Microsoft Sentinel product updates.
In a hurry? Jump straight to your section of interest!
Jump to a section:
- New Microsoft product names
What is Microsoft Sentinel?
Microsoft Sentinel product updates
Microsoft Sentinel & security alert reduction
Conclusion
As some of you may have noticed, we now have some great weather for going to the beach or putting your BBQ grill to work. Summer is a wonderful season for change and now it’s time to embrace changes to some of Microsoft’s security products.-
Related Blogs
Office 365 Nonprofit – Which License Should You Choose?
Microsoft 365 Nonprofit Price Changes with Added Value
-
New Microsoft product names
With these changes, Microsoft might be looking to capitalize on the strength of its main branded keyword “Microsoft”. The specific products have not changed (only their product names). The table below will help you avoid any confusion if you stumble upon any of the new product names during your busy day.
-
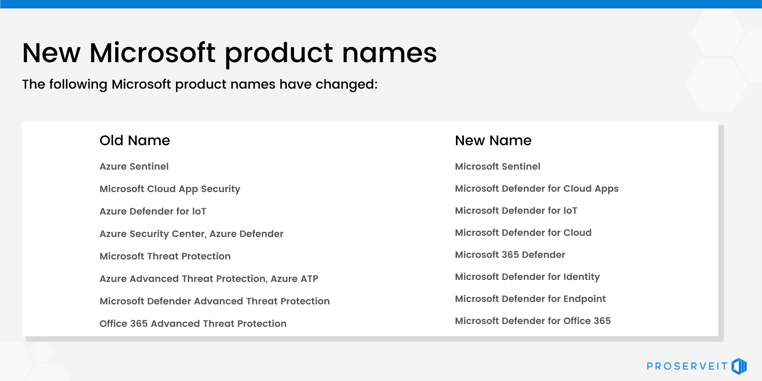 It is important to update any of the following names especially if they appear on your current website or content pieces (i.e. whitepapers, eBooks, PowerPoint templates).
It is important to update any of the following names especially if they appear on your current website or content pieces (i.e. whitepapers, eBooks, PowerPoint templates). For those who want a refresher, below is a brief overview about Microsoft Sentinel (formerly known as Azure Sentinel).
What is Microsoft Sentinel?
Microsoft Sentinel is a cloud-native platform that helps you detect, investigate, and respond to advanced threats across your entire digital footprint. This solution provides smart threat intelligence and protection analytics for enterprise-level organizations, delivering a specific solution for threat visibility, proactive hunting, attack detection, and threat response.
With Microsoft Sentinel in your environment, you can do the following:
💻 Collect: Microsoft Sentinel collects your data across all your users, devices, applications, and infrastructure.
🔍 Detect: Microsoft Sentinel uses AI (Artificial Intelligence) to help you identify anomalies and threats so you can investigate and respond quickly.
🕵️ Investigate: Microsoft Sentinel provides a unified workspace for security analysts so they can collaborate, investigate threats, and speed up response time.
⚙️ Respond: Microsoft Sentinel gives you the tools you need to quickly contain and remediate threats across your environment.
Microsoft Sentinel integrates with Microsoft Defender for Endpoint (formerly known as Microsoft 365 Advanced Threat Protection), which includes an endpoint protection solution that uses Microsoft Endpoint Manager to protect your devices from malware and other threats.
Microsoft Defender for Endpoint is included in Microsoft 365 E5, but you can also purchase it as a standalone subscription. Microsoft 365 E5 includes all the features of Microsoft 365 E3 (plus additional features).
As Microsoft continues to improve its Sentinel product and there are 2 new updates that every Microsoft Sentinel user will want to be aware of. Read the section below to learn more.
What’s new with Microsoft Sentinel?
Cyberthreats are growing and constantly evolving. In order to keep your environment safe, it’s important to get the latest cybersecurity defenses. Microsoft Sentinel (formerly known as Azure Sentinel) has a team of security engineers behind it and is frequently updated to provide the highest level of protection. These updates are provided to all existing license holders. >>>
Here are 2 new product updates for Microsoft Sentinel:
-
Relate Alerts to Incidents
- You can now manually or automatically add alerts to, or remove alerts from, existing incidents. This new capability will help you refine the scope of an investigation as it unfolds. For example, relate Microsoft Defender for Cloud (formerly Azure Security Center) notifications with those coming from third-party products like FireEye’s Mandiant product line in order to better understand individual threats and vulnerabilities. Use this feature from the investigation graph, the API (Application Programming Interface), or through automation playbooks.
Click here to learn more about this update.
-
Similar Incidents
- The context for incidents in your SOC (Security Operations Centre) can be highly beneficial when triaging or investigating an issue. Other occurrences involving the same entities, for example, can provide helpful context that will assist you to make the best decision faster. On the incident page, there's now a new tab that highlights other incidents that are similar to the one you're investigating. The following are some examples of typical uses for comparable incidents:
- Tracking down other occurrences that could be linked to a wider attack.
- Using a similar situation as a model for handling an incident. The manner in which the last issue was handled can serve as a guide for dealing with this one.
- Seeking advice or consultation from relevant persons in your SOC who have dealt with similar occurrences.
Click here to learn more about this update.
How can Microsoft Sentinel help your organization? Read the section below to see how a professional services organization used Microsoft Sentinel to solve its security alert issues.
How Microsoft Sentinel helped ABM Industries reduce the number of analyzed security alerts by 50%
A leading facilities solution provider, ABM Industries, was experiencing issues related to security alert fatigue.
According to Tech Target, security alert fatigue refers to “an instance where an overwhelming number of alerts causes an individual to become desensitized to them”. Exposure to such a large volume of alerts could lead to important alerts being miscategorized, ignored or given a delayed response. This represents a cybersecurity issue as an important alert can be ignored or missed by a security team dealing with more alerts than they can manage.
Its large global workforce of 140,000 employees required a varied and mobile response as well as a change in its mindset regarding current security needs.
Concerned about this security gap, ABM Industries reached out to ProServeIT for help with rectifying this issue on a permanent basis.
Using outsourced security operations in tandem with internal security analysts, ABM Industries adopted Microsoft Sentinel, automated its security responses (using Microsoft Sentinel’s machine learning capabilities) and reduced the number of alerts the staff needed to analyze by 50%.
This means that the security team at ABM Industries now has more time to tackle any important alerts with increased vigilance and clarity.
Last Thoughts
Maintaining vigilance when it comes to cyberthreats is crucial for the security of your organization. The new updates for Microsoft Sentinel will help users to better analyze past incidents and use those insights to create future mitigation strategies.
Unsure about what to do with your current Microsoft security products? Does your organization need help with its cybersecurity? Click this link to get in touch with one of our experts today.
Tags:

June 10, 2022




Comments