Why Managed IT Services Aren't Complete Without Integrated Cybersecurity
In today's digital era, cybersecurity is paramount for organizations worldwide. However, navigating the landscape of security operations is no small feat, given the escalating complexity and volume of threats, coupled with a shortage of skilled analysts and a lack of seamless integration among security tools. It's no wonder 71% of organizations invest more in AI and machine learning for cybersecurity than just two years ago.
Now, envision a solution that transcends the conventional challenges of cybersecurity. Have you ever thought about taking your security measures to the next level with a steadfast ally at your side? Look no further than Microsoft Security Copilot – the ultimate game-changer in cybersecurity.
ProServeIT has achieved a significant milestone by securing a position as one of the top ten global partners in the Microsoft 365 Copilot Early Access Pilot Program. As a key player in this initiative, ProServeIT is at the forefront of advancements that will reshape the digital transformation landscape. Let's explore the potential of Microsoft Security Copilot together, empowering your organization to navigate security operations seamlessly and proactively stay ahead of threats. Join us on this transformative journey in the ever-evolving field of cybersecurity!
In this blog, you will find:
🤔 What is Microsoft Security Copilot?
⚙️ How Does Security Copilot Work?
🔗 Leveraging Microsoft Security Products with Copilot
📒 Microsoft Security Copilot Deploying Scenarios
🤖 Accessing Microsoft Security Copilot: Early Access and Beyond
What is Microsoft Security Copilot?
Microsoft Security Copilot is an essential tool in the security sphere. It takes data signals from various sources, such as Microsoft Defender Threat Intelligence, Microsoft Sentinel and Microsoft Intune, to pinpoint threats proactively and automate responses for rapid threat resolution. Integrating a specialized language model with dedicated capabilities amplifies its utility while allowing it to monitor potential cyber risks effectively.
-1.png?width=762&height=196&name=Security%20Copilot%20(1)-1.png) Security Copilot also helps organizations by boosting the productivity of existing security teams through bridging skill gaps, providing ongoing risk assessments, and offering custom recommendations that help bolster overall cybersecurity posture when dealing with looming issues or possible attacks.
Security Copilot also helps organizations by boosting the productivity of existing security teams through bridging skill gaps, providing ongoing risk assessments, and offering custom recommendations that help bolster overall cybersecurity posture when dealing with looming issues or possible attacks.
The Features of Security Copilot
Microsoft Security Copilot comes well-equipped with a multitude of advanced features designed to revolutionize your cyber defence strategy:
⏲️ Real-Time Threat Intelligence
Microsoft Security Copilot is a valuable tool that leverages Microsoft's extensive global threat intelligence. With over 65 trillion daily signals, it detects indicators of compromise and provides incident data for inquiries. It also offers plugins that access authentic sources like Microsoft Defender reports and related articles, which ensures top-notch protection against cyber threats with up-to-date information from Microsoft's specialists.
☁️ Proactive Cloud Environment Monitoring
Microsoft Security Copilot is crucial for ensuring cloud environment security. It offers comprehensive monitoring and detection services to help IT teams identify potential threats early. Artificial intelligence quickly detects anomalies, unusual behaviour, malicious activities, and vulnerabilities, maximizing data protection. With proactive monitoring, organizations can safeguard their systems against cyber risks efficiently.
🔎 Advanced Detection and Response
Microsoft Security Copilot offers advanced detection capabilities powered by a robust large language model (LLM), resulting in faster reactions and improved safety. It is crucial to address potential threats by providing comprehensive data on situations that may expose organizations to recognized dangers.
Security Copilot provides step-by-step instructions to help analysts handle incidents, identify risks, and gain thematic intelligence from Microsoft's global threat intelligence feed. This ensures swift identification of newly detected or anticipated actions by malicious actors, enabling effective maintenance of security postures.
The Benefits of Using Security Copilot
Experience heightened monitoring capabilities by harnessing tools like Microsoft 365 Defender – a standout benefit among many. With its precision-driven capabilities, this innovative system introduces novel approaches that amalgamate signals for enhanced performance. These tech-driven measures are pivotal in ensuring safety within the sector.
Enterprises worldwide, regardless of their resource constraints, can now tap into valuable insights on digital defence, thanks to the empowering solutions provided by Microsoft Security Protection Copilot. Here’s how Microsoft Security Copilot propels your security strategy:
✅ Swift Threat Detection and Response: Automate analysis, investigation, and remediation processes for faster and more efficient threat management.
✅ Enhanced Visibility and Control: Attain a comprehensive view of your security posture through intuitive dashboards, detailed reports, and timely alerts.
✅ Simplified Operations: Reduce costs and complexity with a unified platform seamlessly integrated into your existing security tools and workflows.
How Does Security Copilot Work?
Microsoft Security Copilot is a powerful AI-driven tool that uses two separate AI models to secure data and automate threat detection and response. The Microsoft Copilot conversational interface processes prompts submitted by the user through its “grounding” process, meaning it accurately understands each prompt to tailor answers relevant to their requirements. This precise prompting system gives users more specific information to help them act accordingly. The following steps summarize how Copilot works:
Microsoft Security Copilot: How it works
☑️ Dual AI Models in Action:
Security Copilot utilizes two AI models for robust data security and automated threat detection and response.
☑️ User-Friendly Conversational Interface:
It engages the Microsoft Copilot conversational interface, ensuring an accurate understanding of user prompts through a "grounding" process and providing tailored answers specific to user requirements.
☑️ Operational Process:
User prompts trigger the language model within Security Copilot to provide an initial answer, which undergoes post-processing to refine the solution before delivering the refined solution back to the user, completing one cycle within Microsoft's security infrastructure automation engine.
☑️ Synergistic AI Model Functions:
The language model simultaneously handles data protection, amplifies activity-based automated defence mechanisms, and ensures accuracy and efficiency across all cybersecurity operations.
☑️ Rule-Based Operation:
It operates within Microsoft's security infrastructure, guided by comprehensive rulesets, involves application metadata functioning at fully enabled levels, and is managed correctly for safety and performance.
☑️ Organizational Integration:
It is implemented seamlessly from the highest executive ranks to organizational teams, referenced against multiple sources to ensure safety thresholds.
☑️ Query Validation:
It validates query complexity metrics against field conditions to ensure the achievement of expected results while maintaining a balance between safety and performance.
Leveraging Microsoft Security Products with Copilot
Microsoft Security Copilot offers a seamless integration with various Microsoft security products, including Microsoft Defender, Microsoft Sentinel, and Microsoft Intune, which enhances its overall cybersecurity capabilities. Organizations can achieve a comprehensive and secure approach to managing and monitoring their systems by leveraging these products. Let's explore how these integrations amplify the benefits of Security Copilot:
%20(1).png?width=762&height=382&name=Microsoft%20Copilots%20(1)%20(1).png)
Strong Integration with Microsoft Defender XDR
Microsoft Security Copilot integrates with Microsoft Defender XDR, offering advantages like incident summarization and script/code analysis. The platform also provides threat intelligence and leverages generative AI for investigations, enhancing security against evolving threats. This creates unified end-to-end protection with Microsoft Security solutions, especially in preventing critical data exposure from external threats.
Seamless Integration with Microsoft Sentinel
Microsoft Security Copilot seamlessly integrates with Microsoft Sentinel to manage SIEM, XDR, and threat intelligence tasks in one place through the Defender portal. This integration includes Microsoft Intune for a comprehensive security system. Combining these platforms offers device protection, data safety, improved compliance, and streamlined processes. Security Copilot and Microsoft Sentinel collaborate to provide real-time analysis and response services for security alerts and incidents through dedicated monitoring modules.
Device and Access Management with Microsoft Intune
Microsoft Intune is a cloud-based security solution that enhances device and access management. It enforces policies, remotely manages devices, controls access to company resources, and distributes apps. It integrates with Microsoft Security Copilot to provide natural language commands for identity and device management. Users can analyze drafts before deployment and perform 'what-if' analyses. This synergy between Security Copilot and Microsoft Intune allows effortless access to data related to user devices, enabling organizations to handle their IT infrastructure better using trusted Microsoft services.
Data Protection with Azure OpenAI Architecture
Microsoft Security Copilot employs strong security controls to ensure users' data privacy using its advanced enterprise compliance framework. It integrates with Azure OpenAI securely without compromising Microsoft 365's details or storing any associated information in Azure OpenAI. This enables powerful processing through this service while protecting user data at all times and guaranteeing their safety.
Microsoft Security Copilot Deploying Scenarios
Microsoft Security Copilot has various deployment scenarios for securing organizational IT infrastructure. Here are some of the scenarios:
Scenario Spotlight: Incident Response
Microsoft Security Copilot integrates with incident response workflows to provide security teams with actionable insights from other Microsoft products. Its threat intelligence capabilities enable faster identification of potential threats, while its predictive powers anticipate malicious activity and ensure compliance with audits. This proactive and efficient approach improves organizations' security processes by utilizing real-time analysis of alerts related to known threats, eliminating the need for manual execution by team members.
Scenario Spotlight: Compliance Monitoring
Microsoft Security Copilot simplifies compliance monitoring in cybersecurity. It can help businesses maintain network security, adhere to strict regulations and protocols for data protection, implement risk management controls, and meet Azure production data standards according to HIPAA requirements. The access control features ensure that all individuals only have access to the information they are authorized to view using dependable underlying measures of safeguarding data privacy with Microsoft Security Copilot at the helm.
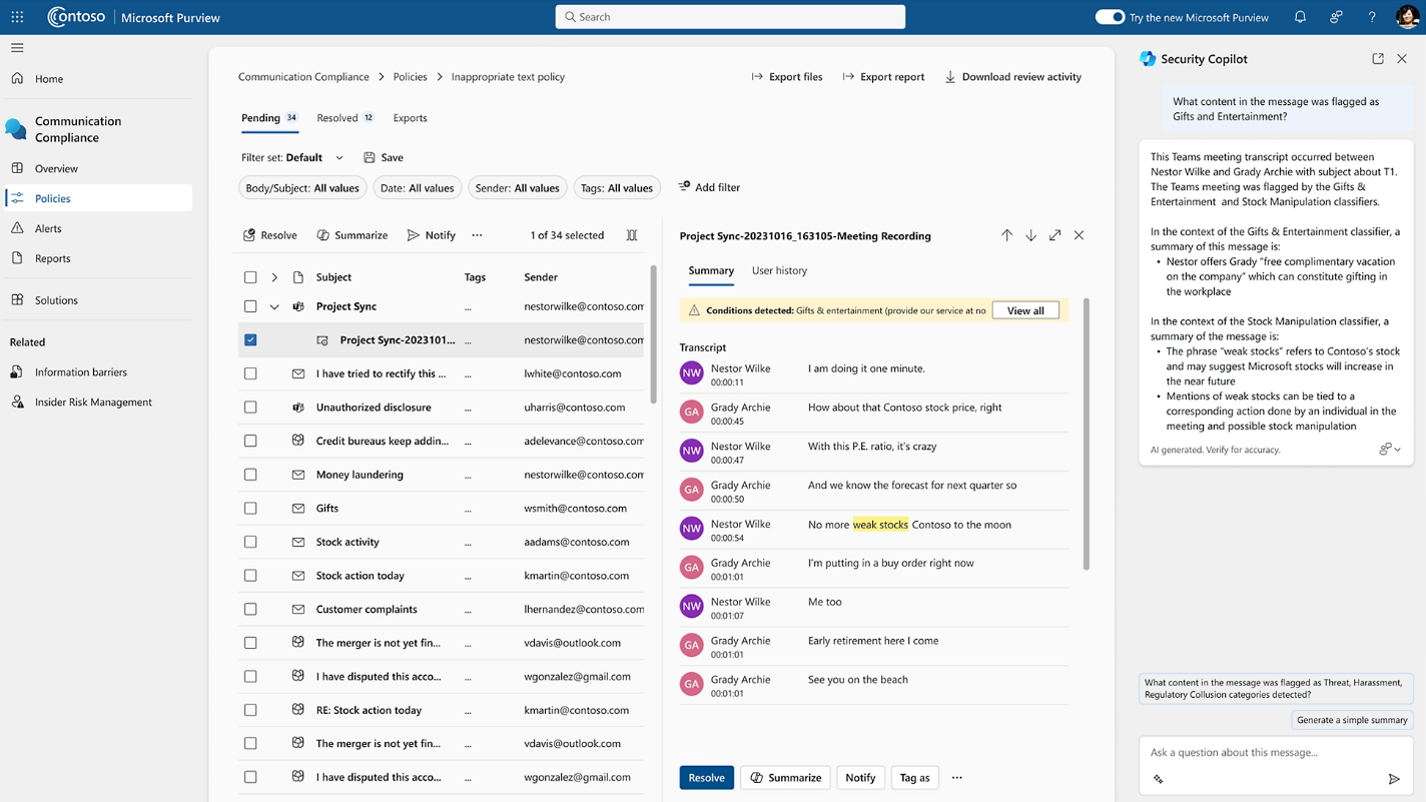
Scenario Spotlight: Vulnerability Management
Microsoft Security Copilot plays a crucial role in vulnerability management. It collects real-time security data from endpoint devices and servers to identify software versions and compare them with threats from intelligence feeds. Utilizing AI and NLP powered by GPT technology, it provides efficient instructions for tackling cyberattacks quickly. This benefits users of all levels, from novices to professionals, in managing dangerous situations effectively. Microsoft Security Copilot automates patching vulnerable software, ensuring timely updates for maximum safety against breaches.
You can also learn about Microsoft Copilots:
4 Strategies for Business Leaders to Integrate AI into Tech Roadmaps
ls Your Company Ready for Microsoft 365 Copilot? 5 Must-Do Actions
5 Steps to Adopt Microsoft Sales Copilot for Your Business
Accessing Microsoft Security Copilot: Early Access and Beyond
Microsoft Security Copilot is in its early access phase, providing a selected group of users, individuals and businesses with the opportunity to explore and utilize its impressive features.
Is cybersecurity vulnerability keeping you up at night?
ProServeIT helps enterprises fortify their defences with cutting-edge security measures.
If that sounds familiar, let's talk. Strengthen your cybersecurity today!
Explore advanced cybersecurity with the Microsoft Security Copilot Early Access Program. Organizations can contact account representatives for eligibility and enjoy six months of in-depth exploration, including demonstrations and educational sessions. As we anticipate the full release, Microsoft Security Copilot is set to revolutionize threat detection in real-time, leveraging AI technology and user feedback to fortify network defence mechanisms. Stay tuned for updates on the impending full release from Microsoft.
Conclusion
As organizations prepare for the imminent release of Microsoft Security Copilot, it is crucial to understand its features and benefits. Preparedness is key to unlocking its potential and harnessing its power for enhanced security. Stay tuned for updates and be ready to leverage the full potential of Microsoft Security Copilot in enhancing cybersecurity measures.
 Unlock the full potential of Microsoft Security Copilot with ProServeIT's exclusive Readiness Assessment. Ensure your organization is well-prepared to harness the transformative power of this advanced tool. Book a meeting with us now to tailor your security measures based on your business requirements and objectives. Secure your future with ProServeIT's Microsoft 365 Copilot Readiness Assessment – because proactive cybersecurity starts with readiness!
Unlock the full potential of Microsoft Security Copilot with ProServeIT's exclusive Readiness Assessment. Ensure your organization is well-prepared to harness the transformative power of this advanced tool. Book a meeting with us now to tailor your security measures based on your business requirements and objectives. Secure your future with ProServeIT's Microsoft 365 Copilot Readiness Assessment – because proactive cybersecurity starts with readiness!
.webp?width=120&height=120&name=Hyun%20Blog%20(1).webp)
December 29, 2023

.png?width=500&height=500&name=cyber%20security_110110543%20%5BConverted%5D%20(3).png)


Comments