When it comes to IT Security, 2017 was not a good year for many people. It seemed like both organizations and individuals were under attack. Ransomware, data breaches, and security vulnerabilities made headlines all around the globe. So, it’s hardly a wonder that IT security will be a hot button issue going forward into 2018.
In this blog, it’s all about how you can protect your organization. Read along to learn about some great IT security tools you should consider using, and to understand the importance of doing a Cyber Security Assessment.
Best IT Security Tools to Use in Your Organization
Below, we’ve compiled a list of several IT security tools that you can use in your organization. We should note that this isn’t an exhaustive list – there are other products out there – but these are the ones that we deal with on a regular basis. Want to know more about these tools and have hands-on experience with them? Our 5-day workshop is the best way to explore the tools! Sign up today >>
1. Windows 10

With built-in features like Windows Hello, Microsoft Edge, and SmartScreen, Windows 10 is being heralded as Microsoft’s most secure operating system. Windows 10 protects your users’ identities, information, and devices from threats with several threat protection and security management tools. Windows Defender Antivirus, Exploit Guard, System Guard, Application Guard, and Application Control all work together to remove or defend against attack vectors used by hackers.
2. Enterprise Mobility + Security
A comprehensive Cloud solution, Microsoft Enterprise Mobility + Security (EM+S) helps your organization to address the constantly-changing cybersecurity landscape. EM+S safeguards your organization’s resources, helps you track suspicious login activity, allows you to gain a deeper understanding of your user, device, or data activities, and gives you the power to change permissions when necessary.
Including such things as single sign-in access to your corporate resources from any device, EM+S is your answer for improved security across Cloud, on-premises, or mobile devices.
3. Azure Active Directory Identity Protection
Attackers are increasingly effective in using sophisticated phishing attacks to steal a user’s identity and gain access to your environment. And, as soon as a hacker gains access – even if it’s someone low on the corporate ladder – it’s relatively easy for them to gain access to more important content.
Azure Active Directory Identity Protection, therefore, helps protect your organization by allowing you to configure risk-based policies that will automatically respond to detected issues if the risk level you specified has been reached. Using the adaptive machine learning algorithms and heuristics that detect suspicious incidents or anomalies, Azure Active Directory Identity Protection generates both reports and alerts, which will let you evaluate what issues have been detected, and take the necessary actions to either mitigate or remediate the threat.
4. Windows Information Protection
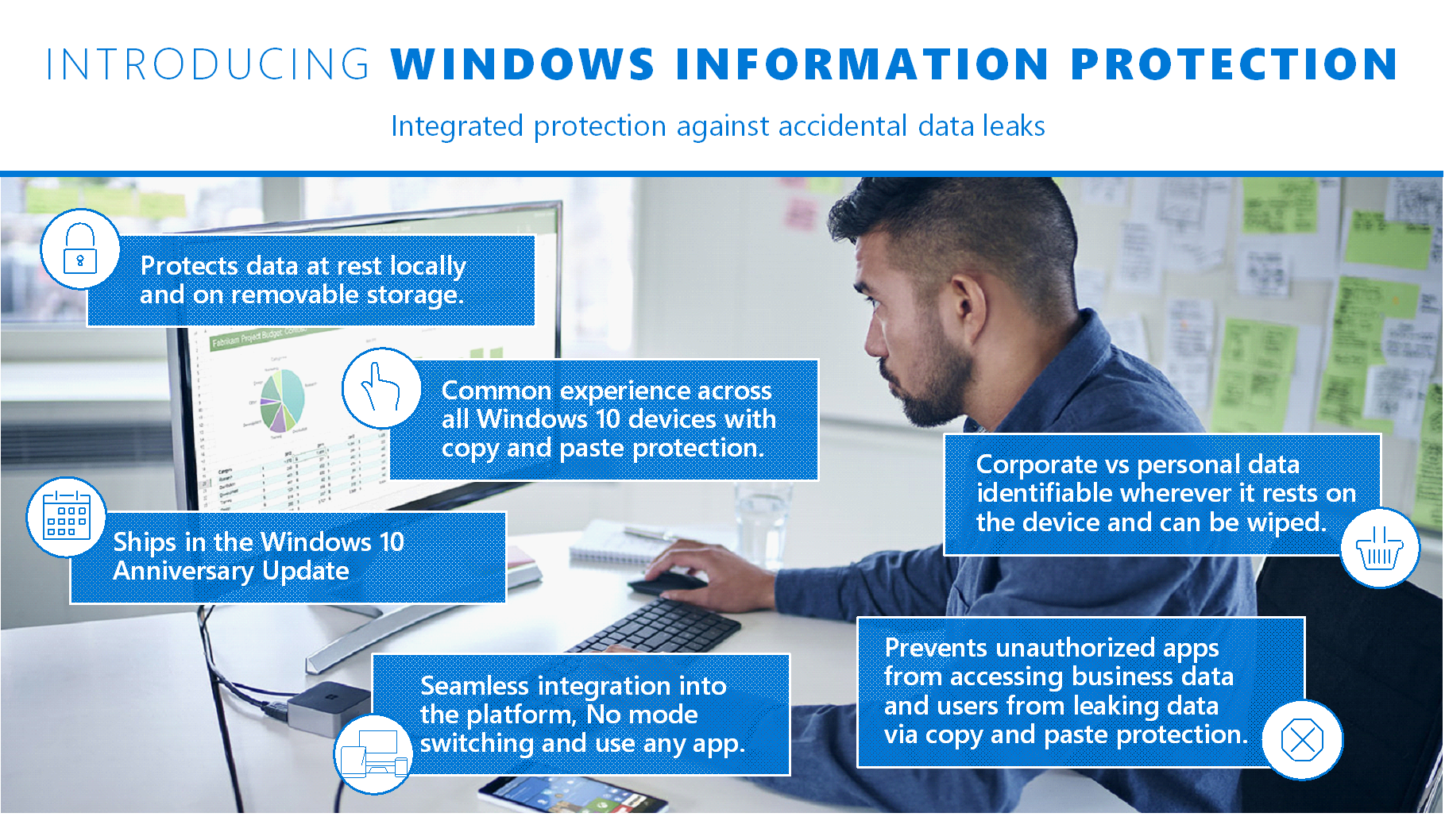
Windows Information Protection (WIP) was introduced as a part of the Windows 10 Anniversary Update. Windows Information Protection integrates with other Microsoft products like Office 365 and Azure Rights Management to identify personal and business information, determine the apps that can access it, and provide basic controls to help determine what you can do with business data (for example, restricting the ability to copy and paste data to an unsecured location).
WIP is a behind-the-scenes, easy-to-deploy solution that doesn’t get in the way of user experiences. It has been designed to prohibit corporate data from leaking into personal or public domain (unless your IT department chooses to implement a policy allowing it). Simply put, WIP ensures that only authorized users and aps are accessing your business data.
5. Office 365 Advanced Threat Protection (ATP)
With capabilities like Safe Links (proactively protecting your users from malicious hyperlinks in email messages), Safe Attachments (protecting you from unknown malware and viruses), Spoof Intelligence (detecting senders who are spoofing your domain by pretending to be someone else in your organization), Quarantine, and advanced anti-phishing capabilities, Office 365 ATP helps protect your organization’s email, files, and Office 365 applications from any unknown malware or viruses.
Available as an add-on to many of the Exchange and Office 365 subscription plans, Office 365 ATP helps you gain critical knowledge of who in your organization is being targeted, which users are clicking on malicious links, and investigate which messages have been blocked because of unknown viruses or malware.
Interested in Office 365 ATP? You can add it to your Office 365 subscription for a minimal fee of $2.40 CAD per user per month. Contact us and we will help you get it set up.
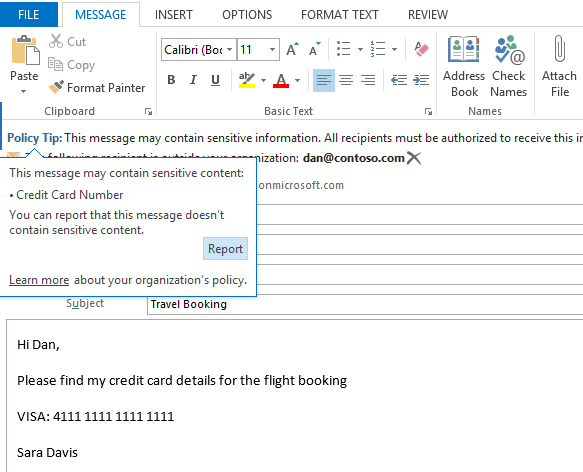
6. Office 365 Data Loss Prevention
No organization wants their users to pass along sensitive information. With Office 365 Data Loss Prevention, you can empower your user to be more conscious about your company policies surrounding the sharing of sensitive information (like credit card information, or information that’s travelling outside of your organization). Your email administrators can set up policies through the Exchange Administration Centre in the Office 365 admin portal that will tell the Office 365 Data Loss Prevention tool to scan through your user emails in the background. If the tool determines that a policy is about to be breached, a Policy Tip will pop up in the email window that alerts your users that they are about to pass on sensitive information.
IT Security Tool 7 – Office 365 Advanced Security Management
Included in the Office 365 E5 (and available to the other Office 365 enterprise plans for a small fee), Advanced Security Management for Office 365 gives you greater control and visibility over your Office 365 environment in these three areas: threat detection, enhanced control, and discovery and insights.
With threat detection, you can set up anomaly detection policies that will alert you of potential breaches in your network. Enhanced control lets you set up policies that track specific activities, like flagging when someone has multiple failed sign-in attempts, someone downloads more data than they usually do, or someone signs in from an unknown or risky IP address. And with an app discovery dashboard that lets your IT professionals see your organization’s Office 365 and other Cloud services usage, you can maximize your investments in IT-approved solutions. Plus, you can determine if there’s any shadow IT (tech that you haven’t explicitly approved) activity occurring within your organization.
IT Security Roadmap Workshop – Gain Hands-On Experience with the IT Security Tools
Workshops, like our 5-day IT Security Roadmap workshop, are designed for organizations just like yours to take steps towards enhancing your overall security. These workshops provide you with hands-on experience of the tools we’ve discussed in this blog (and others), giving you valuable insight into how they can best protect your organization.
But it’s not just about the hands-on experience. These workshops also allow you to look at where you currently are with topics like identity & assess management, information protection, and threat protection, and look at the various tools that are available to you to improve your security posture. And what organization can’t use that? Interested in doing an IT Security Roadmap workshop? Book your spot at one today!