Why Managed IT Services Aren't Complete Without Integrated Cybersecurity
Since its launch in November 2022, ChatGPT has gained widespread popularity, with over 100 million people worldwide now using it. This AI-powered chatbot has proven to be a highly effective tool for various tasks, from answering complex questions to scheduling appointments. While AI tools like ChatGPT can undoubtedly bring many benefits, there are also valid concerns about the potential risks associated with this technology, particularly in cybersecurity.
In this blog, you will find:
👨🏫 Understanding the Basics of AI and Its Applications in Cybersecurity
🤖 AI-Powered Cybersecurity: Harnessing the Power of Technology for Good
💣 The Pitfalls of Relying on AI in Cybersecurity: Navigating the Risks
🌈 Taking the Next Steps in Cybersecurity
ProServeIT is a Microsoft security solutions partner with deep expertise in Microsoft technologies, helping organizations optimize their cybersecurity solutions with AI-powered solutions like Microsoft Sentinel and Secure Identities and Access workshops. Our commitment to customer success ensures businesses can enhance security, reduce risk, and stay protected against even the most advanced cyber threats.
In this blog post, we'll explore the positive and negative aspects of using AI in cybersecurity, including how it can enhance your security measures and the potential challenges that must be addressed to ensure its safe and responsible use.
Understanding the Basics of AI and Its Applications in Cybersecurity
Artificial Intelligence (AI) is a rapidly evolving technology that has the potential to revolutionize the way we interact with computers and digital systems. AI enables machines to think, learn, reason, and act similarly to humans. By leveraging this powerful tool, organizations can gain deeper insights into their data and improve decision-making processes by automating complex tasks that would otherwise require manual involvement.
What is Artificial Intelligence?
AI refers to machine learning techniques or computer programs that perform tasks that typically require human intelligence, such as understanding natural language, recognizing objects, making decisions, and learning from experience. AI algorithms use various techniques, such as machine learning, deep learning, and natural language processing, to mimic human intelligence and automate complex tasks.
How can AI transform cybersecurity?
• Enhancing Threat Detection - AI-based systems can detect and respond to cyber threats much faster than humans, enabling organizations to identify malicious activities quickly. Additionally, AI-based systems can process large amounts of data in real time, making them more efficient at detecting advanced persistent threats (APTs) and zero-day exploits where hackers attack systems with a previously unidentified vulnerability.
• Automating Incident Response - AI can automate incident response processes by analyzing data from multiple sources and quickly determining the best action. This helps organizations reduce the time it takes to respond to threats, minimizing network disruption and damage.
• Improving Vulnerability Management - AI can scan large amounts of data quickly and accurately identify vulnerabilities. This helps organizations avoid cyber threats by reducing the time it takes to patch security holes. Additionally, AI-powered solutions can detect any suspicious behaviour associated with a particular vulnerability that could indicate a potential attack.
• Enhancing Access Control - AI-powered solutions can be used to ensure that only authorized users have access to sensitive data. Using facial recognition technology and biometric authentication, AI-based systems can verify a person's identity before granting access. Additionally, AI-powered solutions can monitor user behaviour to detect any suspicious activities or changes in behaviour that could indicate malicious intent.
• Enhancing Compliance - AI-based systems can help organizations quickly and accurately ensure compliance with data privacy regulations. By constantly monitoring user activity, AI-powered solutions can identify any potential issues that need to be addressed to remain compliant. Additionally, AI-powered solutions can alert administrators when a regulation is violated or updated.
You may be interested in these blogs:
👍 Cyber Hygiene Best Practices for Secure Workplaces
😈 What is a Ransomware and How to Protect your Organization?
😱 Ransomware Attacks Impact Organizations of All Sizes: 3 Common Myths
AI-Powered Cybersecurity: Harnessing the Power of Technology for Good
AI-powered cybersecurity solutions offer numerous benefits for organizations. By leveraging technology, businesses can improve their security posture, reduce costs, and increase efficiency.
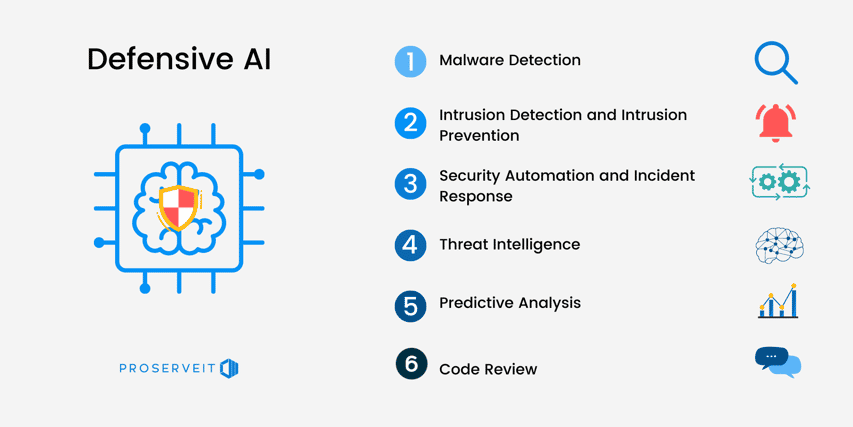
• Malware Detection - AI-based cybersecurity products can quickly and accurately detect known and unknown malware by identifying patterns in malicious software and any new variants that may emerge.
• Intrusion Detection and Prevention - AI technology can monitor network traffic to detect and prevent malicious activities, including zero-day exploits. By leveraging machine learning algorithms, these solutions can quickly identify patterns and suspicious behaviour that could indicate a potential attack.
• Security Automation and Incident Response - AI solutions, such as incident response and vulnerability management, can automate security processes. These automated defensive tools help organizations reduce the time it takes to respond to cyber threats and patch security holes, minimizing network disruption and damage.
• Threat Intelligence - AI systems can continuously monitor the network for malicious activities or suspicious behaviour and analyze data from multiple sources to identify potential threats. Administrators can receive real-time alerts for a timely response.
• Predictive Analysis - AI can use predictive analytics to anticipate future threats and vulnerabilities. These solutions detect suspicious behaviour before it escalates into a cyber attack, keeping the organization ahead of cybercriminals.
• Code Review - AI can review code and identify security vulnerabilities accurately. This helps organizations avoid cyber threats by reducing the time it takes to patch security holes. Additionally, AI can detect any suspicious behaviour associated with a particular vulnerability that could indicate potential future attacks.
The Pitfalls of Relying on AI in Cybersecurity: Navigating the Risks
Although AI-powered solutions offer numerous benefits for cybersecurity, they also present some potential risks..png?quality=low&width=762&height=382&name=8%20Tips%20Main%20(2).png)
• Malware Creation - AI can automate malware creation, making it easier for cyber criminals to launch targeted cyber attacks. Organizations should be aware of this risk and take appropriate measures to protect their networks.
• Smart Botnets - AI-powered botnets can launch sophisticated attacks with minimal effort. Organizations should take steps to detect and protect against these threats, as they can devastate their networks.
• Spear Phishing - AI can launch targeted spear phishing attacks against key individuals like a Chief Financial Officer. This is a particular concern as it can be difficult for traditional security systems to detect these threats quickly. Organizations should implement measures to detect and mitigate such AI-powered attacks.
• Automated Reconnaissance - AI can automate the reconnaissance process, allowing cybercriminals to identify potential targets quickly and easily. Organizations should be aware of this risk and take steps to protect their networks from such attacks.
• Deepfakes - AI-powered deepfakes can be used to deceive individuals and organizations. Organizations should be aware of this risk and take steps to protect themselves by verifying any suspicious content or communications they receive.
• Adversarial Attacks - AI can be vulnerable to adversarial attacks, which could allow cyber criminals to bypass security systems or manipulate data. Organizations should ensure they have measures to protect themselves against such cyber attacks.
Taking the Next Steps in Cybersecurity with ProServeIT
As a Microsoft security solutions partner, ProServeIT offers security assessments to identify vulnerabilities and provide recommendations. We also provide Microsoft-funded workshops and a Security Operations Centre-as-a-Service (SOCaas) solution called Alarm Guardian for 24/7 monitoring and alerts, empowering businesses to protect against cyber threats.
A Guide to Security Assessments
The first step to improving your organization's security is to assess your current security posture by comparing it to the security baseline. This will help identify gaps and potential risks your organization is exposed to. Once these risks are identified, we can create an actionable plan to prioritize and mitigate them, helping to improve your organization's overall security.
 To improve your organization's security, you should assess your security practices, discover your Security Maturity level, develop an actionable plan to address identified risks and understand the costs and ROI of investing in security. Contact us today here, and let's find your security baseline.
To improve your organization's security, you should assess your security practices, discover your Security Maturity level, develop an actionable plan to address identified risks and understand the costs and ROI of investing in security. Contact us today here, and let's find your security baseline.
Empowering Your Security Journey with Microsoft-Funded Workshops
 The Microsoft Funded Security Workshops are designed to assist you with your baseline and advanced security and compliance priorities and initiatives. Find more detailed information here, and check your eligibility here.
The Microsoft Funded Security Workshops are designed to assist you with your baseline and advanced security and compliance priorities and initiatives. Find more detailed information here, and check your eligibility here.
Introducing Alarm Guardian: Your Comprehensive SOC-as-a-Service Solution
Just like your employees, your company data (i.e. customer information, financial data, intellectual property, etc) is priceless.
 By partnering with our Alarm Guardian service, you can protect your organization's data and technology environment from potential cyber threats. Alarm Guardian is a comprehensive Security Operation Centre-as-a-service (SOC-as-a-Service) solution that provides 24/7 monitoring and alerts, empowering your organization to avoid potential security threats. With Alarm Guardian, you can know that your valuable assets are protected.
By partnering with our Alarm Guardian service, you can protect your organization's data and technology environment from potential cyber threats. Alarm Guardian is a comprehensive Security Operation Centre-as-a-service (SOC-as-a-Service) solution that provides 24/7 monitoring and alerts, empowering your organization to avoid potential security threats. With Alarm Guardian, you can know that your valuable assets are protected.
Content from: ProServeIT Academy 2023 Cybersecurity Course 2 by George Abou-Samra
Edited by: Betty Quon & Hyun-Jin Im
Tags:
May 17, 2023


.png?width=500&height=500&name=cyber%20security_110110543%20%5BConverted%5D%20(3).png)


Comments