Why Managed IT Services Aren't Complete Without Integrated Cybersecurity
The growing number of information security threats combined with the increasing complexity of threats have finally caught the attention of organization leaders. Now it’s not a matter of if you have a security incident, but when. Your ad hoc technology solutions are not adequate enough for today’s threat landscape. Thus, a comprehensive information security strategy and roadmap are absolutely essential to secure your organization’s information and systems.
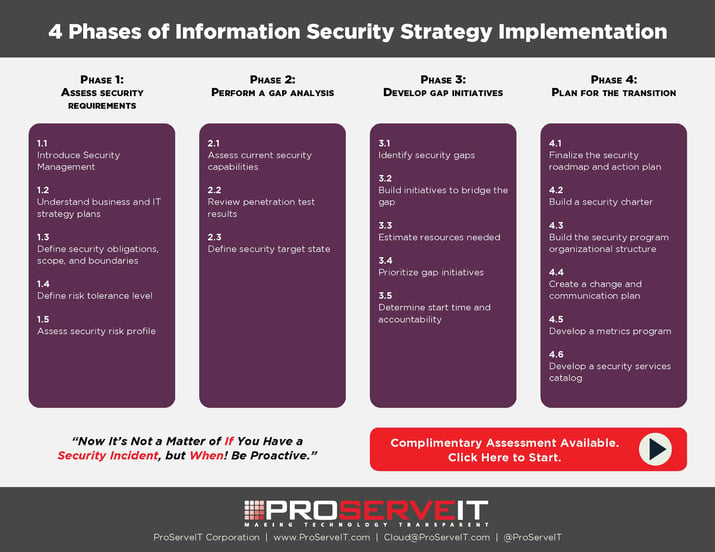
Not sure where to start? You are not alone! It can be overwhelming as there are many things to consider. We suggest the following 4-phase approach when it comes to implementing your organization’s information security strategy:
Phase 1. Assess security requirements
Phase 2. Perform a gap analysis
Phase 3. Develop gap initiatives
Phase 4. Plan for the transition
We have various tips, data, and information for each phase and will share them with you for the next few weeks throughout our blog series.
3 benefits of information security strategy
This blog post is focused on the first step of the phase 1. Assess Security Requirements – introduce information security management. Before we begin the discussion of information security management, let’s consider why organizations need to allocate resources for their information security strategy:
1. Competitive Differentiator
A strong information security strategy can be a competitive differentiator when customers and consumers are selecting products, services, and business partners.
2. Eliminate unnecessary costs and losses
Prevention controls protect critical data and assets from theft and compromise and eliminate costs and losses.
3. Reduce the negative impact
Response processes can limit the impact and associated costs from an eventual attack and potential data compromise.
Conventional vs. New Threats
Organizations today face the full gamut of threat actors. The proliferation of hacking techniques and commoditization of hacking tools has enabled more and more willing people to become threat actors.

Conventional Threats
Conventional threats can be divided into internal and external threats. Employees are the internal conventional threats because they have access and can steal sensitive data or assets. They can do it out of convenience (easy to steal), by selling to a competitor, or in leaving the organization. Also, it is possible that employees accidentally disclose sensitive data. External conventional threats include:
1. Lone Cyber Criminals
Either single actor or small group of actors hacking or scamming. Opportunistic in nature. Commonly motivated by financial gain.
2. Organized crime
Criminal syndicates performing widespread hacking for financial gain. Example: the Russian Business Network operates botnets for spamming and phishing.
3. Former employees
Vengeful or disgruntled former employees will have in-depth knowledge of internal systems (sometimes their user credentials are still active) allowing them to steal.
New Threats

Trends such as APTs have made attacks more sophisticated and difficult to detect than ever before. Here are some of the new threats that are different from the conventional threats we discussed above:
1. Nation States
Nation state hackers carrying out cyber espionage, sabotage, or warfare. Highly advanced actors without limits. Targets foreign government and company secrets.
2. Activist / Hacktivist Groups
Use of hacking as a means to promote political or social causes. Motivated by ideology or political agenda. Targets large organizations that are in opposition to their cause (e.g. oil and gas companies, governments). Anonymous is the most famous hacktivist group.
3. Terrorists
Terrorist organizations using hacking techniques to spread fear and terror. Attacks are designed to be widespread.
4. Competitors
Highly competitive industries have led to digital corporate espionage. Usually third-party hackers are hired.
5. Domestic intelligence services
Government intelligence services are known to perform widespread data collection on its citizen and corporations.
Data breaches are costly!
There are various costs that will harm your bottom line when you experience data breaches: incident detection and escalation costs, notification costs, post data breach costs, and lost business costs.
- Incident detection and escalation costs
Costs associated with forensic and investigative activities, assessment and audit services, crisis team management and communications to executive management and board of directors. Average cost is over $0.61 million per breach.
- Notification costs
Costs related to creation of contact databases, determination of regulatory requirements, engagement of outside experts, postal expenses, secondary contacts to mail or email bounce-backs, and inbound communication set up. Average cost is over $0.56 million per breach.
- Post data breach costs
Costs associated with help desk activities, communications, investigative activities, remediation activities, legal costs, product discounts, identity protection services, and regulatory interventions. Average cost is over $1.64 million per breach.
- Lost business costs
Any costs related to abnormal turnover of customers, increased customer acquisition activities, reputation losses, and diminished goodwill. Average cost is over $3.72 million per breach.
Cost savings brought by an information security strategy
It is thus important to recognize the value of a good information security strategy for your organization. An information security strategy has moved from cost center to business enabler as organizations realize how expensive data breaches can be. An information security strategy historically has fought to prove its value vs. cost. Organizations could not justify the costs because there was little appreciation for the benefits of existing controls and underestimation of potential costs of a data breach. Now information security strategy is being viewed in a new light. Mature organizations are investing substantially in it.
There are both tangible and intangible cost savings to your organization when you implement the right security strategy:
Tangible cost savings
- Cost savings from an incident reduction
- Cost savings achieved by optimizing information security investments resulting in savings from previously misdiagnosed issues
- Cost savings from ensuring that dollars spent on security initiatives support business strategy
Intangible cost savings
- Improved reputation and brand equity achieved through a proper evaluation of the organization’s security posture
- Improved reputation and brand equity achieved through a business continuity plan/business continuity management process that will enable the business to recover faster from disasters
- The continuous improvement achieved through a good security measurement program
- Ability to plan for the future since less security time will be spent firefighting
3 Tips when implementing an information security strategy
1. Remember that organizations are facing constant change from numerous factors
- New technology integration (social media, cloud, digital, big data, etc.) into business processes
- Exponential growth of mobile devices, integrating business and personal
- Cloud adoption across managed services and remote hosting
- Changing regulatory landscape and requirements
2. Build your information security strategy from the bottom up
- Define your security obligations, scope, risk posture, and the complexity of your environment first.
- Develop a holistic view of your security needs before you begin buying technology solutions.
- Ensure that you’re building a comprehensive information security strategy that covers you end to end, nothing more and nothing less.
3. A comprehensive information security strategy considers people, processes, and technologies
- A comprehensive security program includes both governance and management activities that utilize people, processes, and technologies to prevent, detect, respond to, and recover from incidents.
- Ongoing monitoring and performance measurement are also important elements.
Let us help you with your organization’s security!
Having a security plan will make your business more agile. Now is the time to strengthen your organization’s security by implementing an effective information security strategy to remain competitive in today’s world. Remember: now it’s not a matter of if you have a security incident, but when.
Our team of experts have worked with many organizations to help them implement an information security strategy. Contact us today! We will be happy to run a complimentary cloud security assessment for you and discuss how you can improve your organization’s security!
Tags:
January 12, 2017


.png?width=500&height=500&name=cyber%20security_110110543%20%5BConverted%5D%20(3).png)


Comments