How Can Businesses Cut Cloud Costs Without Losing Performance?
The number of cybercrime incidents has increased by 600% since the COVID-19 outbreak.
The sudden shift to remote work has resulted in hasty cloud migration, adoption of inapt security products and solutions, and in some instances, negligence of the “security” aspect all together. About 53 percent of the technology executives who participated in the 2021 Global Digital Trust Insights Surveys indicated that they were not certain whether their cyber spending aligned with their overall enterprise security strategy.
The sophistication of threats and increasing dependency on technologies mean that businesses need to be proactive with creating and managing their cyber security strategy and platforms. A brief operational disruption or downtime can cost a company in many ways – be it financial or reputational. As estimated by the Gartner Group, the average cost for a single minute of downtime is around $5600.
As number of the cyber threats increased, so did the cyber security technologies to prevent and respond to attacks. Choosing the right technologies and solutions to protect your organization is more important than ever. Organizations need scalable and cloud-native solutions like Microsoft Sentinel to improve their security operations. In fact, the latest Gartner’s Magic Quadrant announced Microsoft as the visionary SIEM solution for the year 2021.
What is Microsoft Sentinel? (formerly Azure Sentinel)
Microsoft Sentinel by Microsoft is a scalable cloud native SIEM (Security Information and Events Management) and SOAR (Security Orchestration Automation and Response) product providing a birds-eye view of your organization and a single security solution for alert detection, threat visibility, hunting and threat response.
📈 SIEM: analyze and correlate data logs from all sources and check where and how the breach occurred and its repercussions.
🔒 SOAR: focus on collecting security-related data and streamlining security operations by using playbooks (automated tasks to respond to security breaches/events). For example, if an account gets compromised, what are the steps to follow to make sure it is secure again?
With real-time threat detection and response, Sentinel is an emerging option for organizations looking for end-to-end security solutions and better threat response capabilities across cloud and on-premises data environments.
Related blogs
3 Ways to prevent data breaches in your organization
What can Microsoft Sentinel do?
Microsoft Sentinel provides intelligent security analytics for security teams and helps them deal with the increasing volume of alerts and complex attacks.
✔️ Collect: Data can be collected from different sources including applications, users, systems, on-premises and across multi-cloud infrastructure.
📍 Detect: Analytics and exceptional threat intelligence help minimize false positives and uncover past unidentified threats
🔍 Investigate: Analyze threats with AI and hunt suspicious activities across security networks derived from Microsoft on the MITRE framework
🛡️Respond: Built-in orchestration and automation of common tasks help to tackle threat incidents quickly
How does Microsoft Sentinel Work?
The first step for getting onboard with Microsoft Sentinel is to connect it with your security sources using data connectors. Azure provides out-of-the-box (Azure AD, Microsoft Cloud App Security, Azure 365 Defender, etc.) as well as built-in connectors (non-Microsoft solutions) for data ingestion.
Once the data is connected and ingested through data connectors, it can be visualized and monitored for potential threats and trends using Azure Monitor Workbooks (integration with Microsoft Sentinel). You can either use built-in workbook templates to get quick data insights or even build custom workbooks for interactive reports.
This evaluation creates specific queries which further help set up rule sets or analytics. Analytics minimizes the number of alerts by correlating it into incidents. Incidents are basically a group of related alerts that pose a potential threat, and which can be further investigated and resolved. Custom analytics rules can be created for specific queries or existing rules can be used as templates to detect anomalous behavior across data.
Alerts are further automated for threat response through Playbooks which are basically Azure Logic Apps. A Playbook is a collection of remediation actions which can be run when an alert or incident is triggered. For example, in the case of an account being compromised, a playbook will either revoke access or block the account until the security team is made aware of the breach. Microsoft Sentinel also comes with a powerful hunting and search query functionality that helps to hunt for security threats even before an alert is triggered. Bookmarks for unusual anomalies can also be created while hunting and can be investigated later or shared with other team members.
Alarm Guardian Uses Microsoft Sentinel Protect Your Organization
How can Microsoft Sentinel protect my business?
⚫ With Microsoft Sentinel, companies can leverage next-generation security solutions with unlimited storage capacity and faster deployment. No hassle with infrastructure setup or maintenance or upfront costs. Scalable resources can be scaled up in times of excessive workloads or down based on the needs of an organization.
⚫ It offers seamless data collection from different sources – be it on-premises or cloud, data integration with existing tools and comprehensive analysis of the data security environment. It bridges the gap between the security and management team by providing data on a centralized platform (dashboard).
⚫ Sentinel powered by built-in AI and ML (machine learning) capabilities deliver faster and smarter security analytics and threat response. It also helps in proactive threat hunting, minimizing false positives, quick analysis of correlated alerts and identifying the scope of an entire attack.
⚫ Built-in user and entity behavioral analytics (UEBA) help in identifying threats and their potential impact. Using baseline behavioral profiles of organizations and ML capabilities, Sentinel can detect anomalous behavior, its sensitivity, compromised assets and its impact radius. Based on this, security teams can further prioritize their investigation and incident handling.
How much does Microsoft Sentinel cost?
Microsoft Sentinel provides a flexible and predictable pricing model including pay-as-you-go (default model) and commitment tiers. It is billed based on the volume of data ingested and stored in the log analytics workspace. Microsoft Sentinel and Log Analytics are charged separately based on the selected pricing plan. In the case where the usage exceeds a selected tier, the user will be billed for the ingestion beyond the commitment tier.
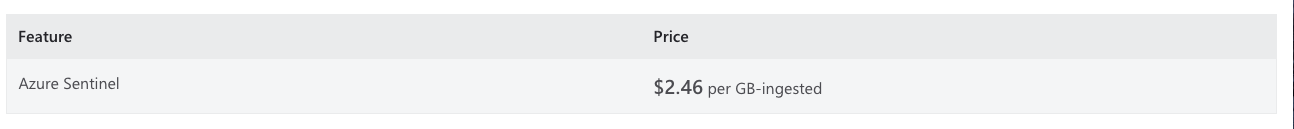
Pay-as-you-go
The pay-as-you-go model includes billing depending on consumption per gigabyte (GB) for the data volume collected for analysis in Microsoft Sentinel and stored in Azure Monitor Log Analytics. The price shown here is standard for analytics enabled by Microsoft Sentinel. It does not cover the related data ingestion charges for Log Analytics. Microsoft Sentinel pricing depends on where you are located in the world as pricing levels differ according to regions and countries.
Commitment Tier:
When choosing the commitment tier, billing is on a fixed fee basis on the selected capacity tier. Companies can save up to 60% on the service cost with a commitment tier as compared to a pay-as-you-go model. Users can either increase or decrease (every 31 days) their commitment tier capacity based on their usage.
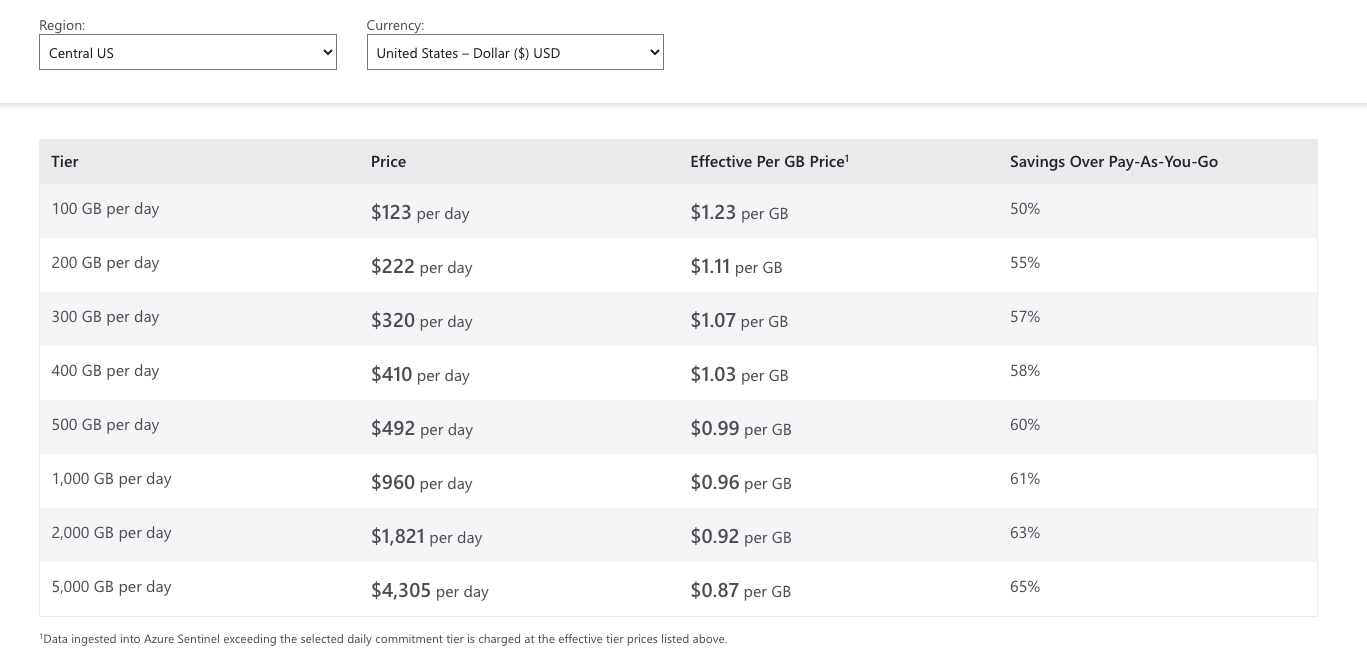 Also, different pricing levels apply to regions across different parts of the world. Price shown here is standard for analytics enabled by Sentinel. It does not cover the related data ingestion charges for Log Analytics (refer to Azure Monitor Log Analytics Pricing).
Also, different pricing levels apply to regions across different parts of the world. Price shown here is standard for analytics enabled by Sentinel. It does not cover the related data ingestion charges for Log Analytics (refer to Azure Monitor Log Analytics Pricing).
Free Trial:
For a risk-free introduction, companies can get a free trial of Microsoft Sentinel for the first 31 days, enabled for no additional cost on Log Analytics workspace, subject to limits including:
For Existing Log Analytics Workspace: For existing workspaces, users can enable Sentinel for no additional cost (any workspace created more than three days ago). Note: The trial period includes charges waived only for Microsoft Sentinel.
For New Log Analytics Workspace: Users can enable ingestion of up to 10 GB/day capacity of log data for the first 31 days at no cost with new workspaces (workspaces that are less than three days old). Note: The trial period includes charges waived for both Microsoft Sentinel and Log Analytics data ingestion and is subject to 20 workspace limits per Azure tenant.
Users will be charged if their usage exceeds these limits and as per the pricing listed on the Microsoft Sentinel pricing page. The free trial also includes additional charges for other automation tools and for your own machine learning tools.
Organizations can retain their ingested data in the workspace at no cost for the first 90 days. Retention prices will be charged as per the standard Azure Monitor Log Analytics after a period of 90 days.
What is the best way to start with Microsoft Sentinel? (formerly Azure Sentinel)
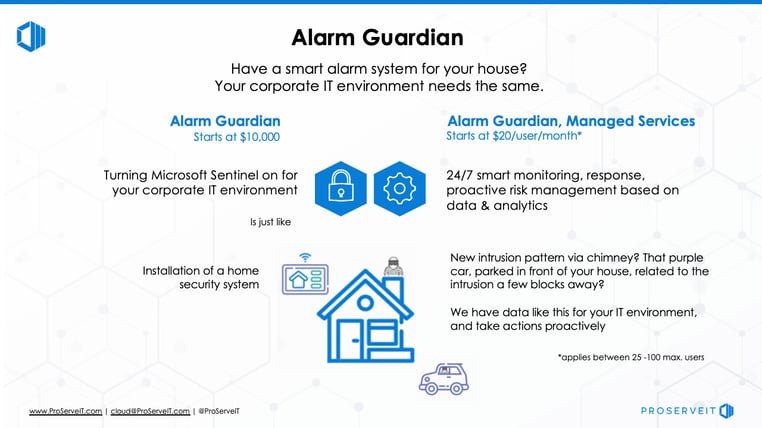
For security to be imbued at every level of your organization, you need a reliable security strategy, a trusted partner, and a smart alarm system for your IT environment. Deployment of Microsoft Sentinel is just the first step and ongoing monitoring and management of the platform is necessary to take full advantage of it.
With Microsoft Sentinel as the monitoring station, ProServeIT's Alarm Guardian is the ultimate managed cybersecurity solution with advanced threat intelligence that protects your digital assets 24 x 7 x 365. With a team of experienced cyber security experts’ assistance, you can feel confident with the constant monitoring and response to potential threats while you focus on other priority business operations.
Our Alarm Guardian is a subscription-based solution which becomes your Security Operations Center to monitor, detect, protect, and review incidents on your behalf in real-time. It also provides contextual insights you can use to further defend and assess the impact of security events with fewer false positives and relevant findings. Download the details of the three different packaged solutions for Alarm Guardian. And book a discovery call to get started.
Content from: Cybersecurity Framework Webinar Series by George Abou-Samra
Edited by: Nikita Gill and Betty Quon
Tags:
October 19, 2021




Comments