How Can Businesses Cut Cloud Costs Without Losing Performance?
Is Multi-Factor Authentication effective? Should you really care about MFA security?
When we talk to our customers about MFA security, we typically find that their reactions fit into one of three categories:
- They buy into it immediately, have already implemented it in their organization, and swear by it.
- They’re aware of Multi-factor authentication and are concerned that MFA holds up the login process, or creates a cumbersome user experience.
- They don’t really understand what MFA security is or what its benefits are, and so they’re not really thinking about it at this time.
If you would classify yourself as the second or the third category, this blog is for you. In the next few paragraphs, we’re going to help you explore multi-factor authentication in greater detail, show you the benefits of using multi-factor authentication, and look at some best practices to create a smooth user experience when implementing MFA security in your organization.
What is Multi-Factor Authentication?
Multi-factor authentication is the process of presenting two pieces of authentication methods to prove you are who you say you are when you’re logging into an account. Authentication methods can be determined as:
- Something you Know (a password, a PIN, or a pass phrase),
- Something You Have (a physical thing, like a card or your phone), or
- Something You Are (your fingerprint, a retinal scan, facial recognition, etc.).
In order to qualify as multi-factor authentication, you need to present your credentials from two or three of these categories. The example of multi-factor authentication provided by the U.S. National Institute of Standards and Technology is that of signing into your bank account via an ATM machine. To be able to access your account and your money, you need to use something you have (your bank card), then enter something you know (your PIN). This is MFA Security.
Why is Multi-Factor Authentication Important?
Here’s a brief description about why multi-factor authentication is so important:
By requiring MFA security to get into a user’s account, email, or system, it means that a password becomes practically useless on its own. This is because, even if a threat actor manages to obtain a user’s password, they won’t have the secondary component (that additional authentication method), to access that which they’re trying to get into. So, by setting up MFA in your organization, you are providing your data and applications with an additional layer of protection against these threat actors.
Related: Cybersecurity 101: Your End-Users are the First Line of Defense
Best Practices When Setting Up Multi-Factor Authentication

As mentioned in the introduction, some people find MFA security to be cumbersome - more of a hindrance than a help. And, if your users are more accustomed to just only using passwords to authenticate, implementing MFA without proper change management could very easily make them resistant to this new change you’re trying to make.
Related: An Effective Change Management Process in 4 Easy Steps
Just like any other technology implementation, change management starts with communicating the changes before implementation occurs. You need to make your employees aware of what MFA is, how this is going to affect them, and any potential issues that could come up around the implementation well before you go ahead and enable it.
Four tips for implementing multi-factor authentication
1. Consider how you will deploy multi-factor authentication within your organization.
It seems like this should go without saying, but it’s very important to plan out your move to MFA long before you actually go ahead and do anything. As part of your initial discussion, you should determine how you’re going to roll this out.
- Will you provide your employees with the opportunity to give their feedback on their experiences with MFA?
- How will you settle any technology issues that come up – is your IT department ready to provide the necessary support for your users if and when they run into trouble?
- Also, consider how you’re going to measure the success of this endeavour – will you have specific KPIs in place that will let you know whether or not switching to MFA has been a positive contribution?
If you’re unfamiliar with multi-factor authentication, you may want to consider bringing in an outside organization, like ProServeIT, to lend their expertise in helping you plan out, set up, and execute your MFA project.
2. Consider enabling Conditional Access to control when Multi-Factor Authentication is required.
Conditional Access allows you to create policies around when multi-factor authentication might be required. For instance, you could use conditional access to require MFA if a user is signing in with a personal device or signing in from a new IP address, but allow them to sign in without MFA if they’re signing in from the corporate office they work out of.
3. Ensure a variety of authentication methods to make it easier for your employees to choose an MFA option that works for them.
Especially when it comes to multi-factor authentication, a one-size-fits-all approach is not something that you want to force your users into adopting. Forcing people to choose text messages as a method for authentication only works if every single employee has reliable access to a mobile device. So, to ensure that your employees can actually make use of the MFA security you’re putting into place, be sure to provide a variety of authentication methods and allow them to choose the ones that work for them.
4. Evaluate your MFA Security on a regular basis.
If there’s one thing we’re sure of, it’s the fact that the threat landscape of today is undergoing constant change. So, when implementing a technology that aims to help with your security posture, it’s important to evaluate it on a regular basis to ensure it’s still doing the job of protecting you! Conducting regular assessments of your MFA security (we recommend at least once a year) lets you know if multi-factor authentication is still working for your organization and shows you if it’s continuing to meet your unique needs and requirements.
How You Can Implement Multi-Factor Authentication
If you are a current Microsoft user, multi-factor authentication comes as a part of the following Azure and Office 365 offerings:

Azure Active Directory Premium licenses
With Azure AD Premium, you get full featured use of Azure Multi-Factor Authentication via the Cloud (with Azure Multi-Factor Authentication Service), or via an on-premises option (Azure Multi-Factor Authentication Server). To help you understand the difference between the two and to determine which is better for your organization, check out this Microsoft article on which version is right.
Related: Securing Your Azure Environment Through Azure Security Center

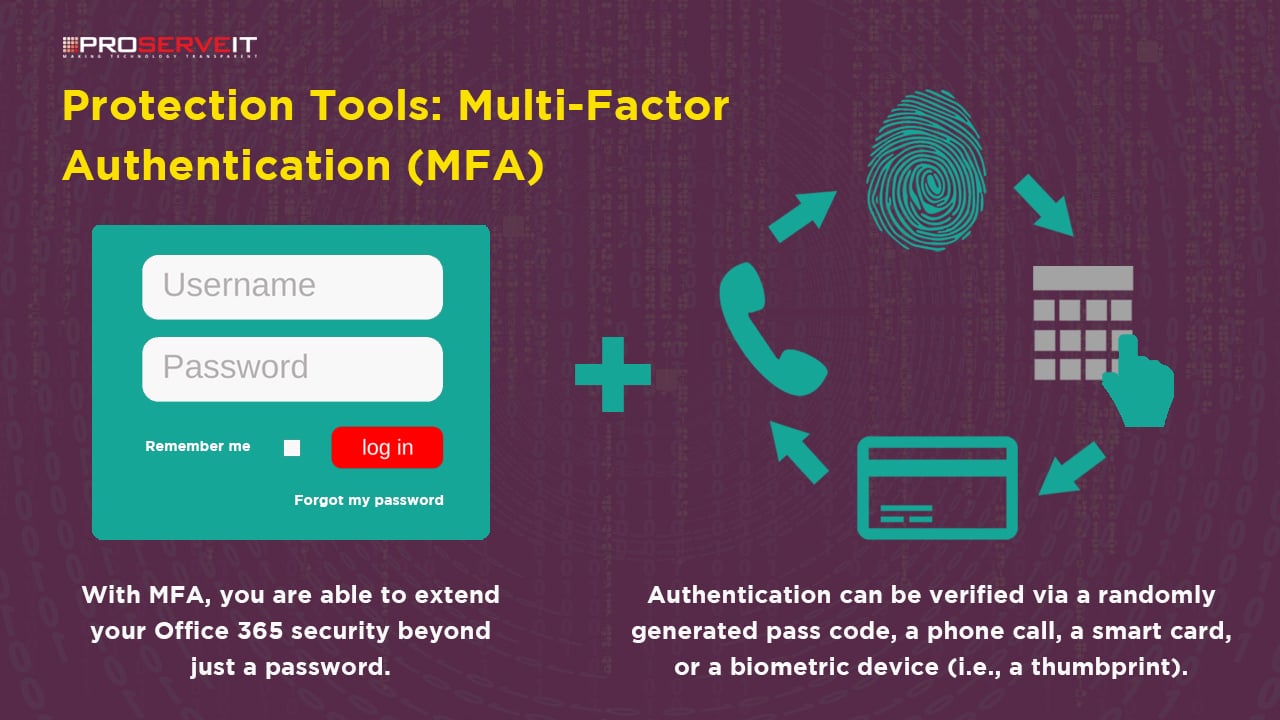
Multi-Factor Authentication for Office 365
Certain Office 365 licenses can use a subset of Azure multi-factor authentication as a part of their subscription. Depending on the Office 365 license you have, you might be able to access multi-factor authentication via your Microsoft 365 Admin Center, and provide your end users with MFA capabilities. If you want to better understand Multi-Factor Authentication for Office 365, we recommend reviewing this comprehensive Microsoft article on it.
Related: A Comprehensive IT Security Policy to Protect Your Organization from Cyberattacks
Enabling Multi-Factor Authentication in Your Organization
As far as we’re concerned, multi-factor authentication is an incredibly beneficial security tool that provides your organization with an added level of security against threat actors of today. However, if not implemented in the right way, it can lead to frustration and headaches for your end users. That’s why we strongly recommend working with an organization that’s familiar with change management best practices.
Our MFA Jumpstart Program can help you implement MFA within your organization to extend your Office 365 security beyond the password on a pilot basis, so that you can determine how best to implement MFA across your organization. We’ll help you set up MFA for Office 365 and conduct a pilot implementation for up to 20 users. At the end of this pilot, you’ll have the required knowledge to fully implement MFA for your remaining users. Give us a shout and get started on your journey to a more secure environment today!
Tags:
May 17, 2019





Comments